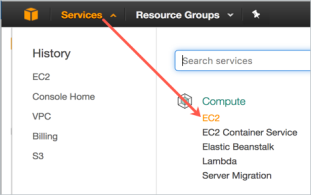
Click Services > EC2.
Deploying a KeyControl node into Amazon Web Services (AWS) requires setting up several components depending on the type of the deployment. The following topics provide step-by-step directions for each of the deployment types, starting with the initial KeyControl node, then adding an Elastic Load Balancer and adding nodes in the same Availability Zone, a different Availability Zone, and a different Region.
| Note: | In addition to encrypting regular data partitions, you can also encrypt your root and swap partitions. Encrypting root and swap partitions ensures that clear-text data never leaves the VM on its way to storage. This prevents virtualization and storage admins from being able to view the data. For details, see Encrypting Root and Swap Drives on AWS. |
To begin with, you need to have an existing account on Amazon Web Services. You will start by logging in to that account.
Click Services > EC2.
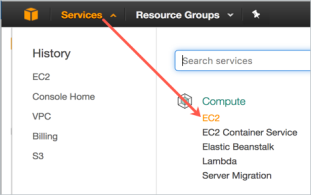
At the top right of the EC2 Dashboard, click your deployment region from the drop-down list. In the example below, US West (Oregon) is chosen, but you should choose based on your needs.
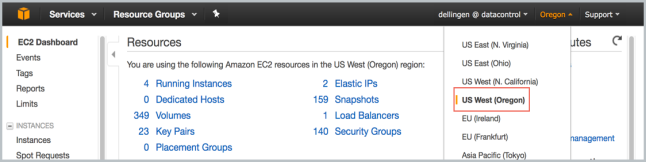
Click Create a Key Pair.
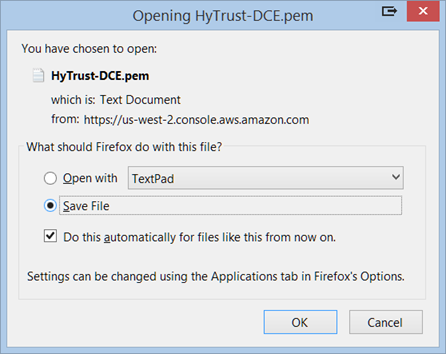
The private key file is created and you may get the option to Open it or Save it. Choose Save File, if you have that option. The likelier case is that it is downloaded automatically. The screen shot below shows the Firefox download dialog box.
The Key Pair is automatically downloaded by your browser as a .pem file into the default download location for your system. Save your .pem file. The base file name is the name you specified as the name of your Key Pair, and the file name extension is .pem. Save the private key file in a safe place; you will refer to it at various points in your interaction with your system.
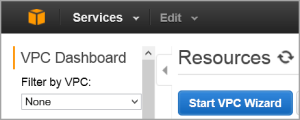
From the VPC Dashboard, click Start VPC Wizard.
Click Select to set up VPC with a Single Public Subnet.
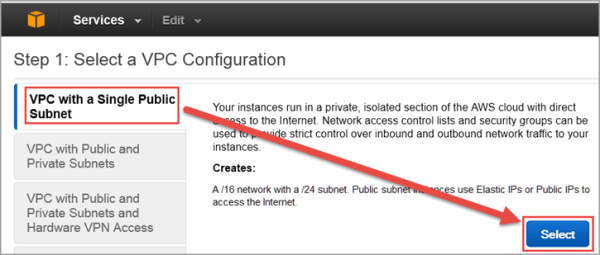
By default, when a VPC is created, an Internet Gateway is automatically assigned to it. If the assigned gateway and/or IP block is insufficient, you can modify the IP block and subnet information according to your needs. You can also create a new Internet Gateway and assign it to your VPC.
| Note: | In order for two VPCs to communicate, there should not be any overlapping IP addresses between the two VPCs. A good example is 50.0.0.0/16 and 100.0.0.0/16. |
Give your VPC a name.
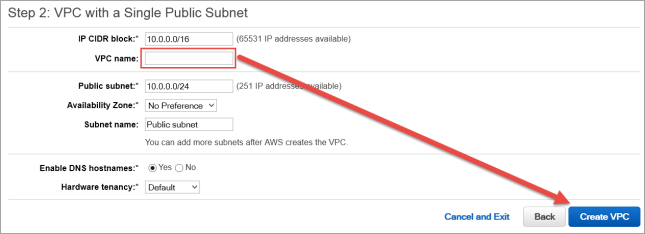
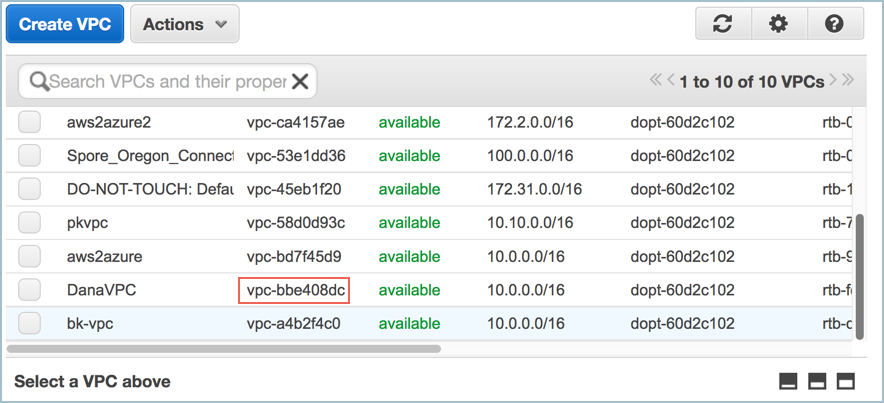
Click Create VPC, and then click OK. Note the VPC ID.
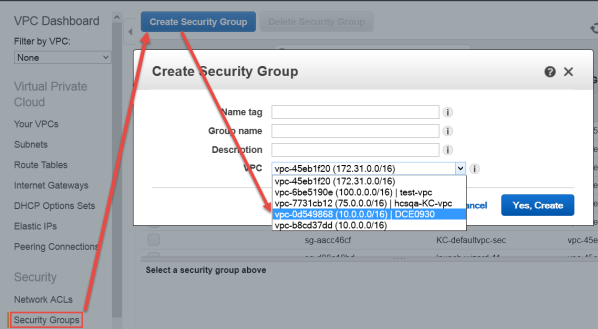
As part of VPC creation a default Security Group is assigned to your VPC. For KeyControl communication, it is recommended to create a Security Group that only enables certain inbound services/ports.
Select the VPC ID from the drop-down list, selecting the VPC that was just created above. Make sure No VPC is NOT selected.
Click the Inbound Rules tab.
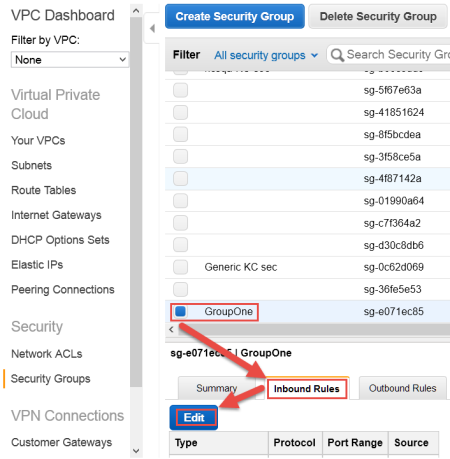
The Edit inbound rules dialog box appears.
For Source, enter 0.0.0.0/0

0.0.0.0/00.0.0.0/00.0.0.0/0The end result should look like this:
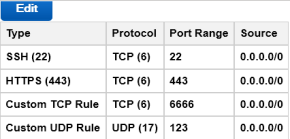
If this KeyControl instance will be deployed in a cluster, the following rules must be implemented in addition to the above list:
The final result should look like this:
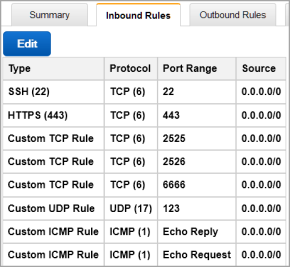
The above is an example of inbound traffic rules for an AWS Security Group. These ports are open to the world, as indicated by their 0.0.0.0/0 CIDR notation, merely for demonstration purposes.
| Important: | It is the responsibility of the administrator to open these ports only to the IP addresses that are absolutely necessary to connect to the KeyControl instance. |
AWS has two separate pools for Elastic IP (EIP) addresses: one pool is for EC2-Classic, and the other for EC2-VPC. It is crucial to allocate the EIP for KeyControl from the EC2-VPC pool.
From the VPC Dashboard (Services > VPC ),click Elastic IPs.
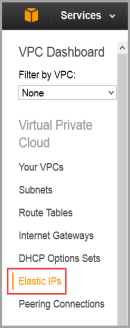
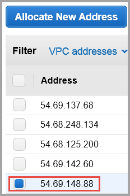
Click Allocate New Address.
It should display that the EIP is for VPC usage and not EC2. This appears in the Scope column.
Click Yes, Allocate. Make a note of the allocated EIP.
From VPC Dashboard, click Launch EC2 Instances.
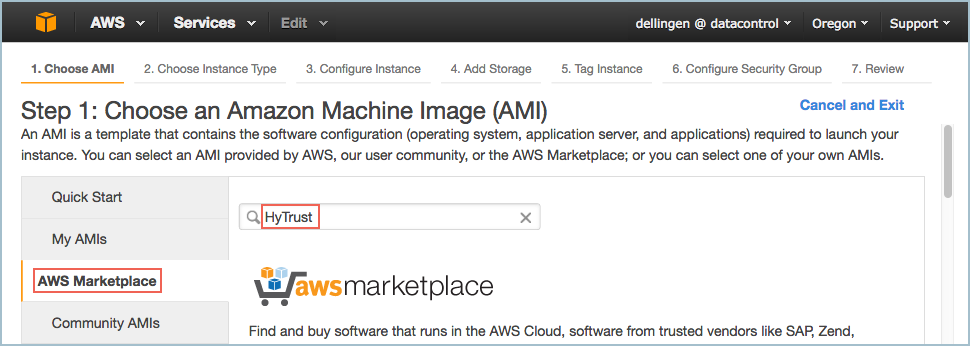
From Step 1: Choose an Amazon Machine Image (AMI) dialog box, click AWS Marketplace, and type HyTrust in the search box. Press Enter:
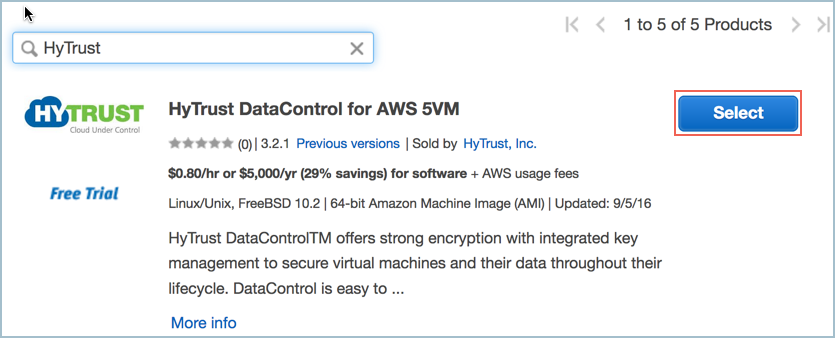
A list of HyTrust DataControl AMIs appears. Read the descriptions, and pick one by clicking Select. For this tutorial, we clicked the first one listed, HyTrust DataControl for AWS 5VM.
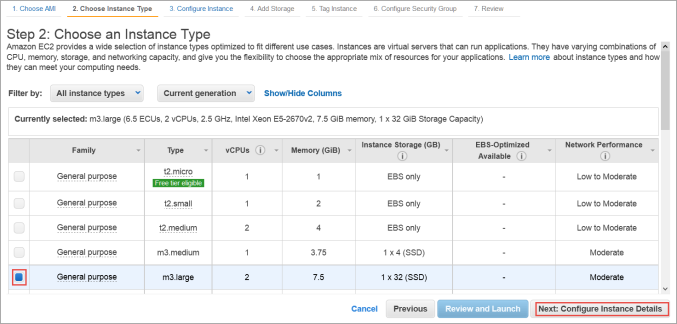
The Step 2: Choose an Instance Type dialog box appears.
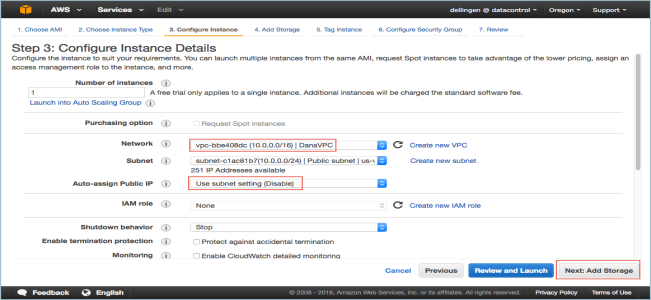
The Step 3: Configure Instance Details dialog box appears.
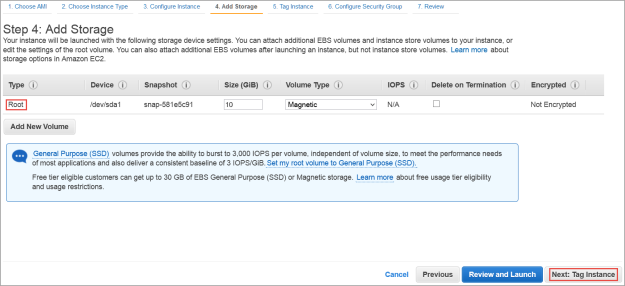
The Step 4: Add Storage dialog box appears.
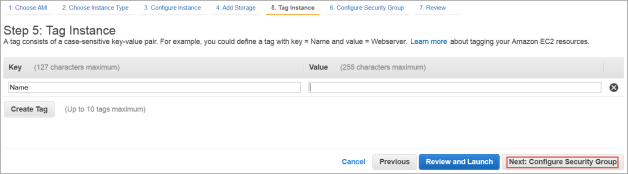
The Step 5: Tag Instance dialog box appears.
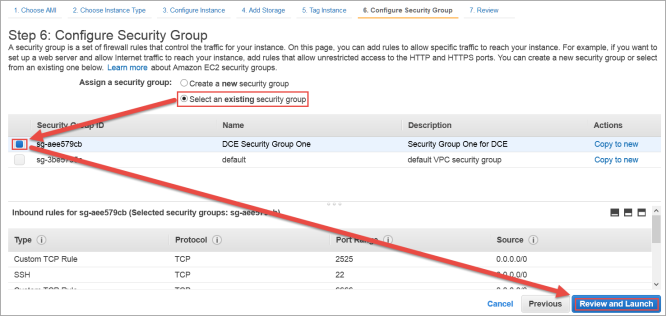
The Step 6: Configure Security Group dialog box appears.
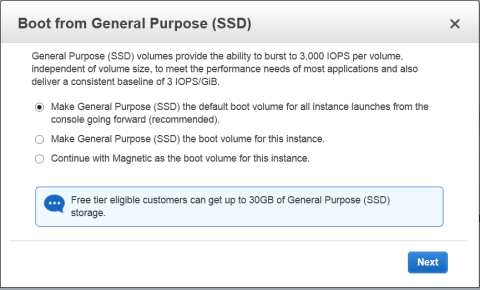
The Boot from General Purpose (SSD) dialog box appears.
The Step 7: Review and Launch dialog box appears.
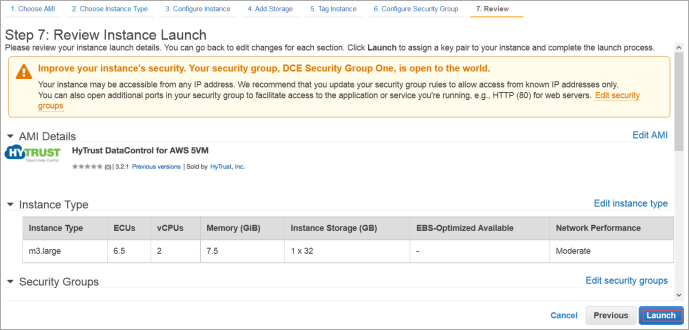
0.0.0.0/0, are "open to the world."
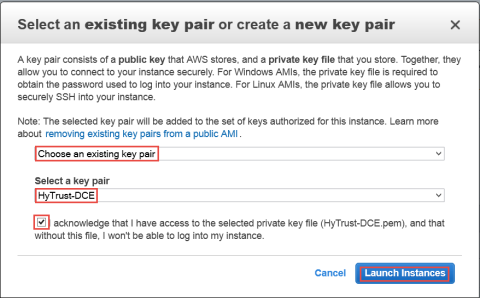
The Select an existing key pair or create a new key pair dialog box appears:
Use ssh to log into the new KeyControl menu system. You will use the key pair associated with the VPC and the EIP associated with the instance. Use the login ID sysmenus. The initial password is sysmenus. Issue the following command from your UNIX shell:
# ssh -i <my_key> -l sysmenus <my_EIP>
You will first be prompted to change the KeyControl menu system's password (you cannot continue to use the initial sysmenus password). You will be required to enter the password twice. Passwords must be a minimum of eight characters.
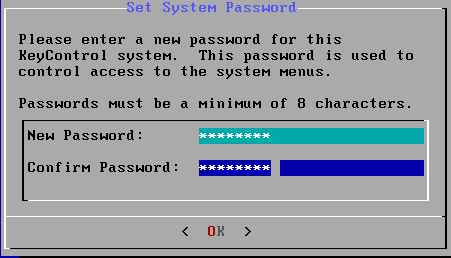
The menus to which the root/password combination enables access are where diagnostics and settings can be manipulated for this system during its lifetime. Without the password, access to the system for these tasks is impossible. It is critical that the password be stored safely somewhere.
Note that this is not a general login account. Since this is a secure node, you cannot get a shell prompt, and only have access to a basic menu system that allows for hardware change, network setup and general debugging capabilities. We cover these topics later.
The last step in configuration is choosing whether you are going to add this new KeyControl instance as a new node to an existing cluster:
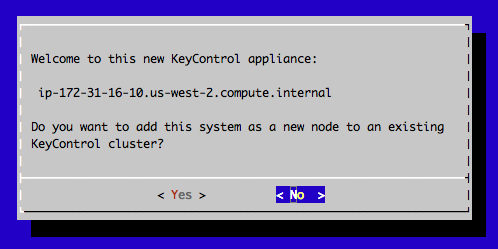
If this is your first KeyControl system and you respond No to this prompt, your system is fully configured and you will see the last of these post-install menus pointing you to the webGUI interface:
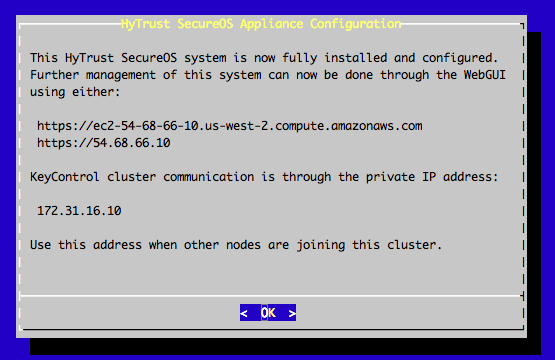
Further configuration takes place in the webGUI.
| Note: | Upgrades for AWS users must be done using the webGUI |