Adding a KeyControl Node to a Cluster in a Different Availability Zone on Amazon Web Services
The following components are required prior to adding a new KeyControl node to an existing KeyControl cluster in a different availability zone:
- One or more running KeyControl servers
- The CIDR block of the VPC or the VPC ID of a running KeyControl server
- The internal IP address of the running KeyControl server
Log on to Amazon Web Services with an existing account
To begin with, you need to have an existing account on Amazon Web Services. You will start by logging in to that account.
For details, see Log on to Amazon Web Services With an Existing Account
Connect to the Same Region as Your Existing KeyControl Server
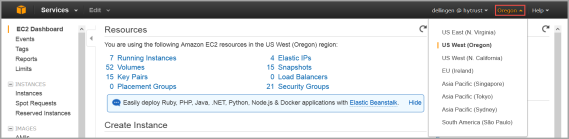
- Log on to your EC2 account.
- Navigate to the EC2 Console Dashboard.
- At the top right of the EC2 Dashboard, click your deployment region from the drop-down list. In the example below, US West (Oregon) is chosen, but you should choose based on the location of your existing KeyControl cluster.
Virtual Private Cloud (VPC)
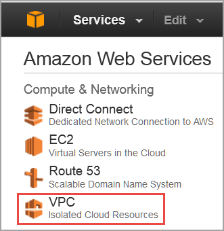
- Navigate to Console Home (yellow cube) at top left of the Dashboard.
- Under Compute & Networking, click VPC (Isolated Cloud Resources).
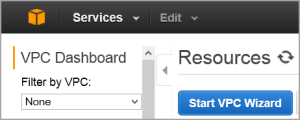
- From the VPC Dashboard, click Start VPC Wizard.
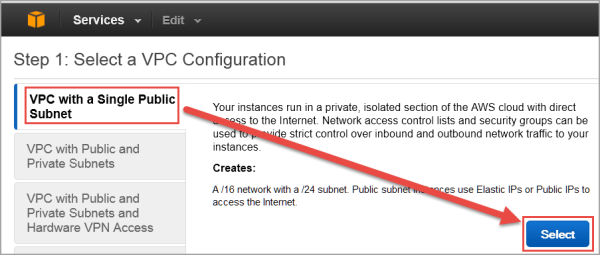
- Click Select to set up VPC with a Single Public Subnet.
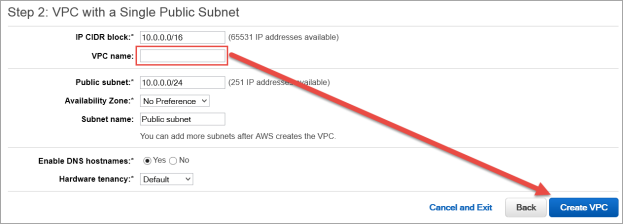
- By default, when a VPC is created, an Internet Gateway is automatically assigned to it. If the assigned gateway and/or IP block is insufficient, you can modify the IP block and subnet information according to your needs. You can also create a new Internet Gateway and assign it to your VPC. Note: In order for two VPCs to communicate, there should not be any overlapping IP addresses between the two VPCs. A good example is
50.0.0.0/16and100.0.0.0/16. - Give your VPC a name.
- Click Create VPC, and then click OK. Note the VPC ID.
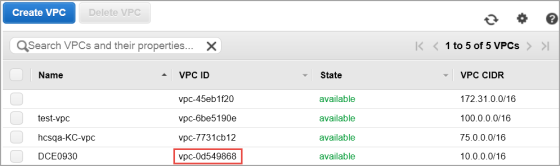
Use VPC Peering to Connect the Two VPCs
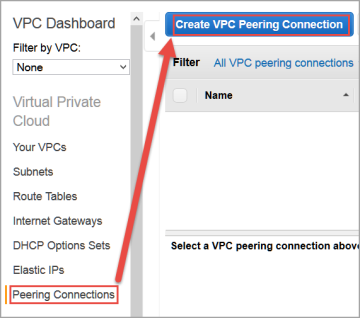
- Navigate to Peering Connections in the VPC Dashboard in the target AWS account.
- If both VPCs belong to the same account, stay in the existing account.
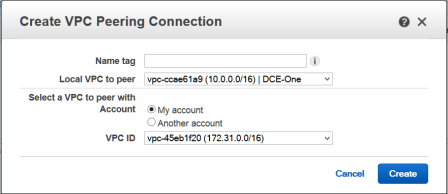
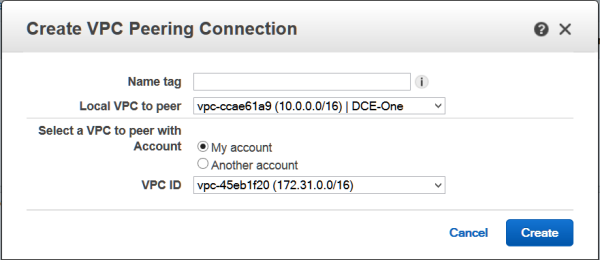
- Click Create VPC Peering Connection. The Create VPC Peering Connection dialog box appears.
- Give your Peering Connection a name, and click Create.
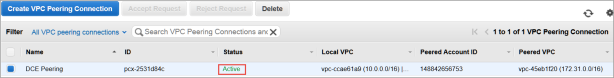
- The Peering connection should indicate that it is pending acceptance.
- Click OK, and then click Accept request.
The state of the peering connection changes to Active.
Modify the Routing Tables of the VPCs
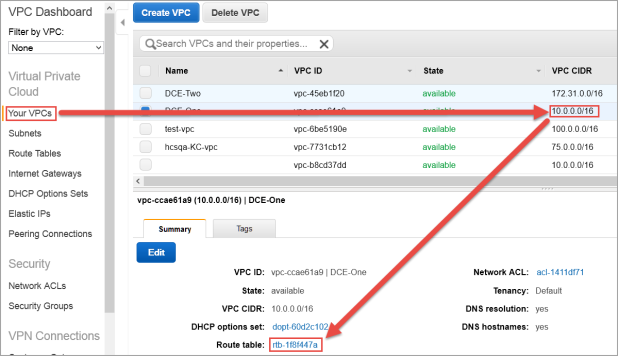
Modify the main routing table of both VPCs to route the network traffic to the peering connection ID.
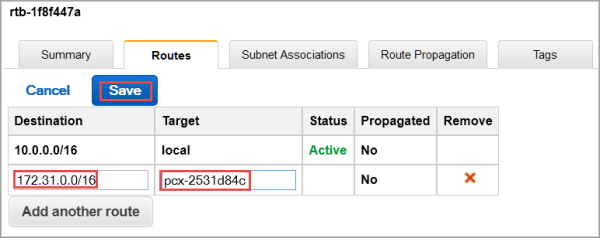
- In the running KeyControl VPC (10.0.0.0/16), navigate to its routing table.
- Click the Route table entry.
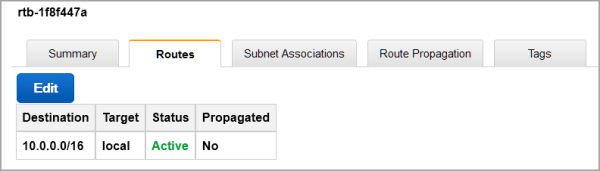
- Click Edit. A line opens up in the entry.
- In the Destination field, enter the CIDR block of the new VPC (172.31.0.0/16).
- In the Target field, click the ID of the VPC peering connection.
- Click Save. Your first routing entry is complete.
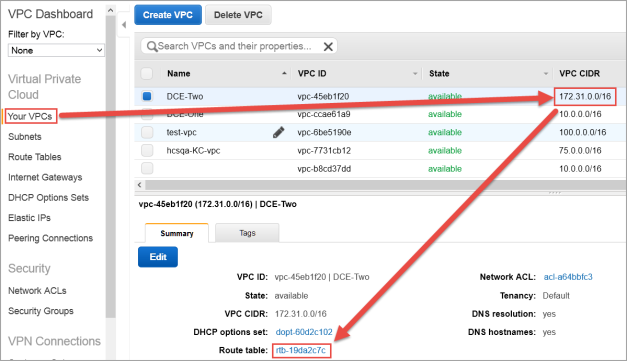
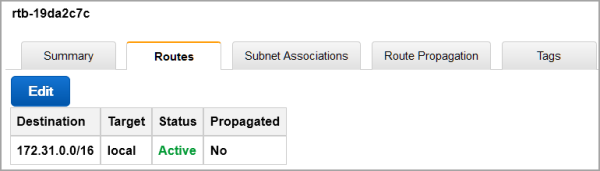
- Next, in the newly created VPC (172.31.0.0/16), navigate to its route table.
- Click the Route table entry.
- Click Edit. A line opens up in the entry.
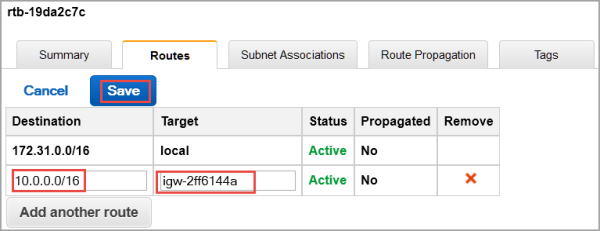
- In the Destination field enter the CIDR block of the running KeyControl VPC (10.0.0.0/16).
- In the Target field, click the ID of the VPC peering connection.
- Click Save. Your second routing entry is complete
Create a Key Pair, if One Does Not Exist
For step-by-step details, see Create a Key Pair.
Create a Security Group, if One Does Not Exist
As part of VPC creation a default Security Group is assigned to your VPC. For KeyControl communication, it is recommended to create a Security Group that only enables certain inbound services/ports.
For step-by-step details, see Create a Security Group.
Add Rules to the Security Group, if Rules Are Not Present
In order to allow communication between KeyControl servers, certain rules must be added to the Security Group of the existing KeyControl cluster.
For step-by-step details, see Add rules to the Security Group.
Create an EIP Address
For step-by-step details, see Create an EIP address.
Launch an instance
- From the VPC Dashboard, click Launch EC2 Instances.
- Click HyTrust AMI from AWS Marketplace.
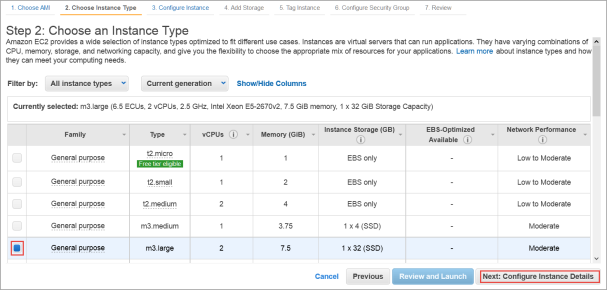
- The Choose an Instance Type dialog box appears.
- From the list of Instance Types, click m3.large or whatever best fits the bandwidth/latency requirements you desire.
- Click Next: Configure Instance Details.
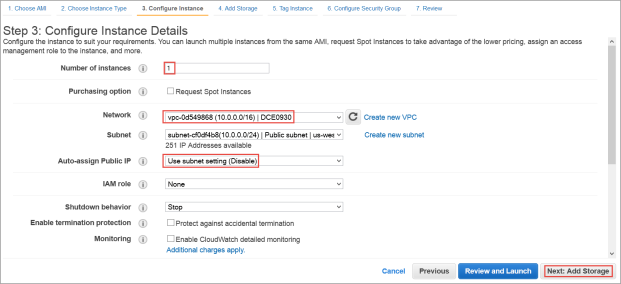
- The Configure Instance Details dialog box appears.
- Click your VPC ID as the Network used for launch.
- Number of instances should be 1.
- Make sure Auto-assign Public IP is NOT set. Click Disable.
- Click Next: Add Storage.
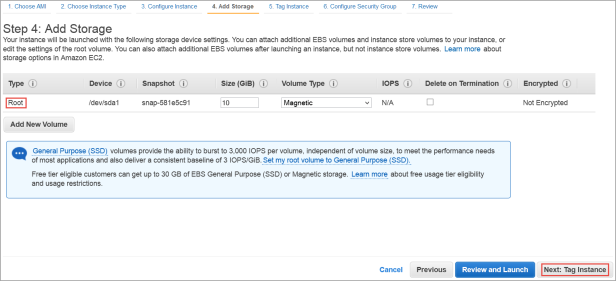
- The Add Storage dialog box appears.
- Root device with all defaults works fine. There is no need to change anything.
- Click Next: Tag Instance.
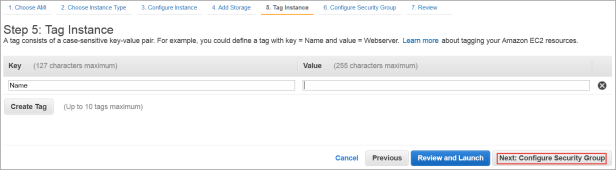
- The Tag Instance dialog box appears.
- If you wish to add key-value tags to your instance, do so.
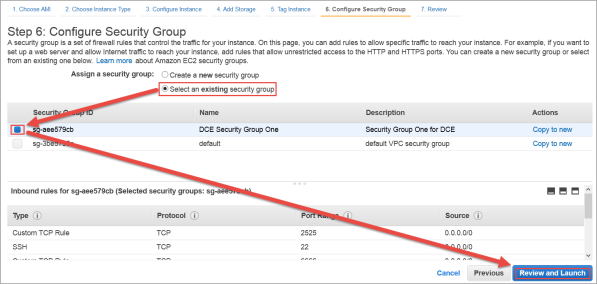
- Click Next: Configure Security Group.
- The Configure Security Group dialog box appears.
- In Assign a Security Group click Select an existing Security Group.
- Select the Security Group of the existing KeyControl node.
- Click Review and Launch.
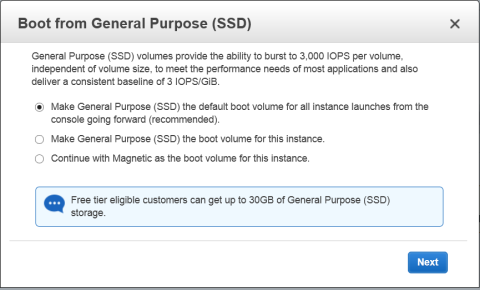
- The Boot from General Purpose (SSD) dialog box appears.
- Click on your choice of boot volume for this instance, and then click Next.
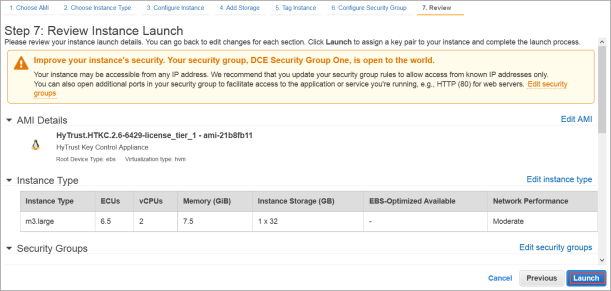
- The Review and Launch dialog box appears.
- Review your settings, paying particular attention to the IP address ranges you have open to external browsers. Your current settings, set at
0.0.0.0/0, are "open to the world." - When you are satisfied with your settings, click Launch.
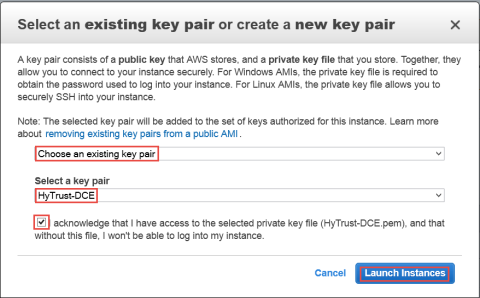
- The Select an existing key pair or create a new key pair dialog box appears:
- When asked to click a Key Pair, click Choose an existing Key Pair.
- Select the Key Pair used for the existing KeyControl node.
- Click the checkbox acknowledgment that you have access to this Key Pair.
- Click Launch instances.

Associate the EIP to the Instance
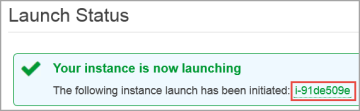
- Once the newly launched instance is in initializing state, note its Instance ID.
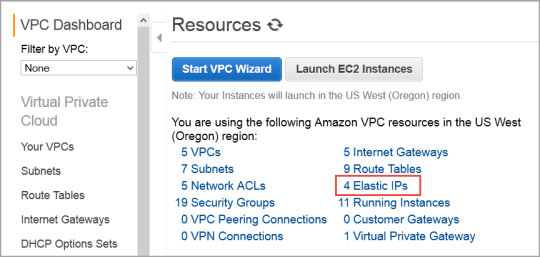
- From the VPC Dashboard, in the center of the screen, click Elastic IPs.
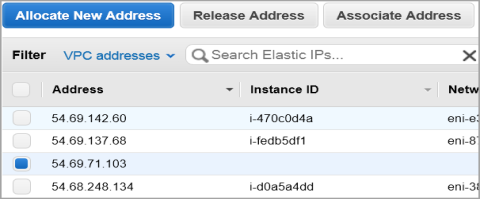
- Click Associate Address.
- The Associate Address dialog box appears.
- In the instance drop-down box, click the instance ID of the new KeyControl node.
- Click Yes, Associate.
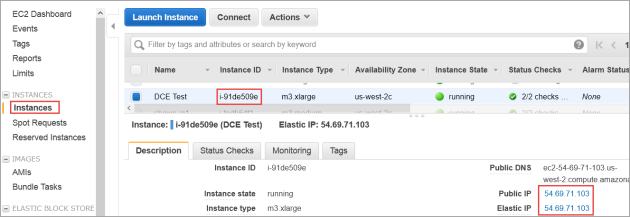
- Click Instances from the EC2 Dashboard.
- Click the Instance ID.
- When the Elastic IP of the instance appears, it indicates that the EIP is now associated with the instance. Note that the public IP has the same address, which you will use after completing the next steps in the KeyControl system menus.
Connect to the Instance Console and Install
Use ssh to log into the new KeyControl menu system. You will use the key pair associated with the VPC and the EIP associated with the instance. Use the login ID sysmenus. The initial password is sysmenus. Issue the following command from your UNIX shell:
ssh -i <my_key> -l sysmenus <my_EIP>- You will first be prompted to change the KeyControl menu system's password (you cannot continue to use the initial
sysmenus password). You will be required to enter the password twice. Passwords must be a minimum of eight characters.
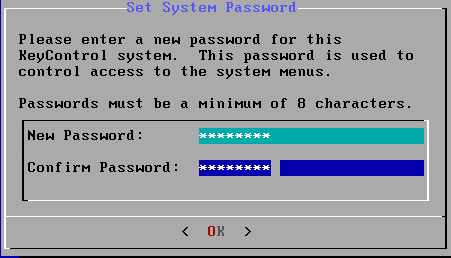
- The menus to which the root/password combination enables access are where diagnostics and settings can be manipulated for this system during its lifetime. Without the password, access to the system for these tasks is impossible. It is critical that the password be stored safely somewhere.
- Note that this is not a general login account. Since this is a secure node, you cannot get a shell prompt, and only have access to a basic menu system that allows for hardware change, network setup and general debugging capabilities. We cover these topics later.
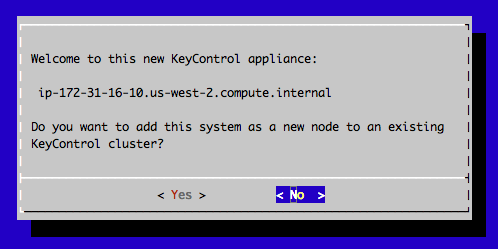
- The last step in configuration is choosing whether
you are going to add this new KeyControl instance as a new node to an existing cluster:
- You do want to add this system as a new node in an existing cluster, so you should click Yes, and follow the directions here: Joining a KeyControl Cluster.
Connect to the GUI of the First KeyControl Node and Authenticate the New KeyControl Node
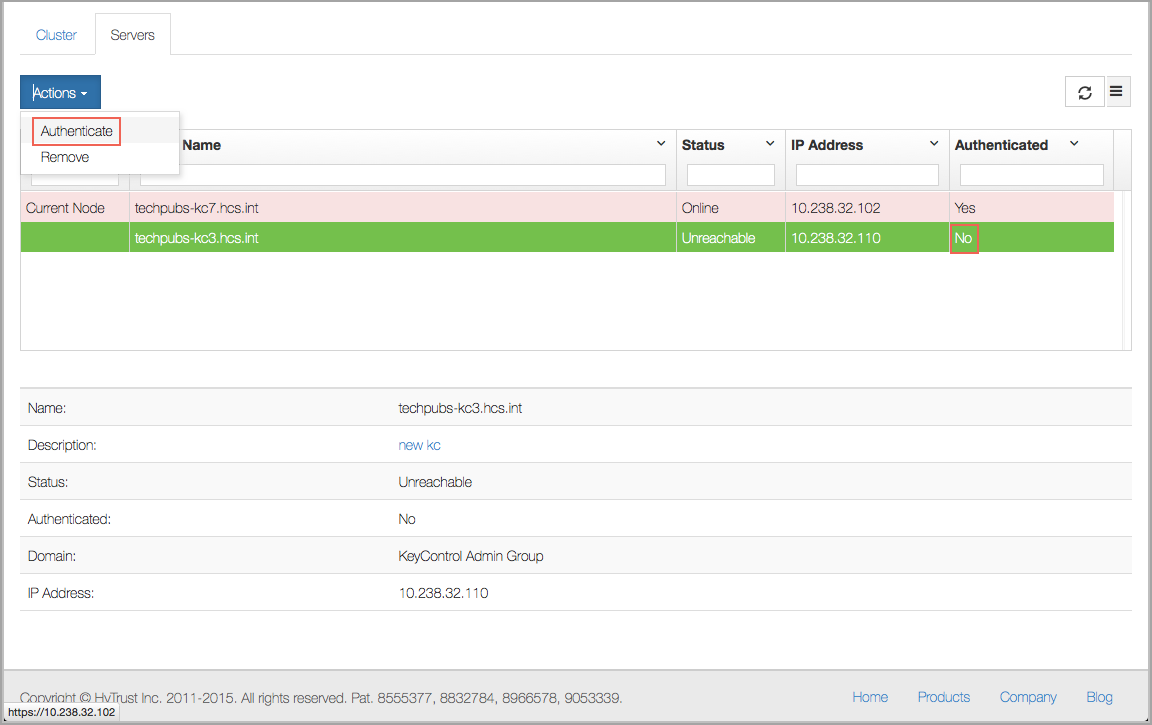
At this point you need to log on to the webGUI of first KeyControl node/cluster with Domain Administration privileges. The new KeyControl node will automatically appear as an unauthenticated node in the KeyControl cluster, as shown below:
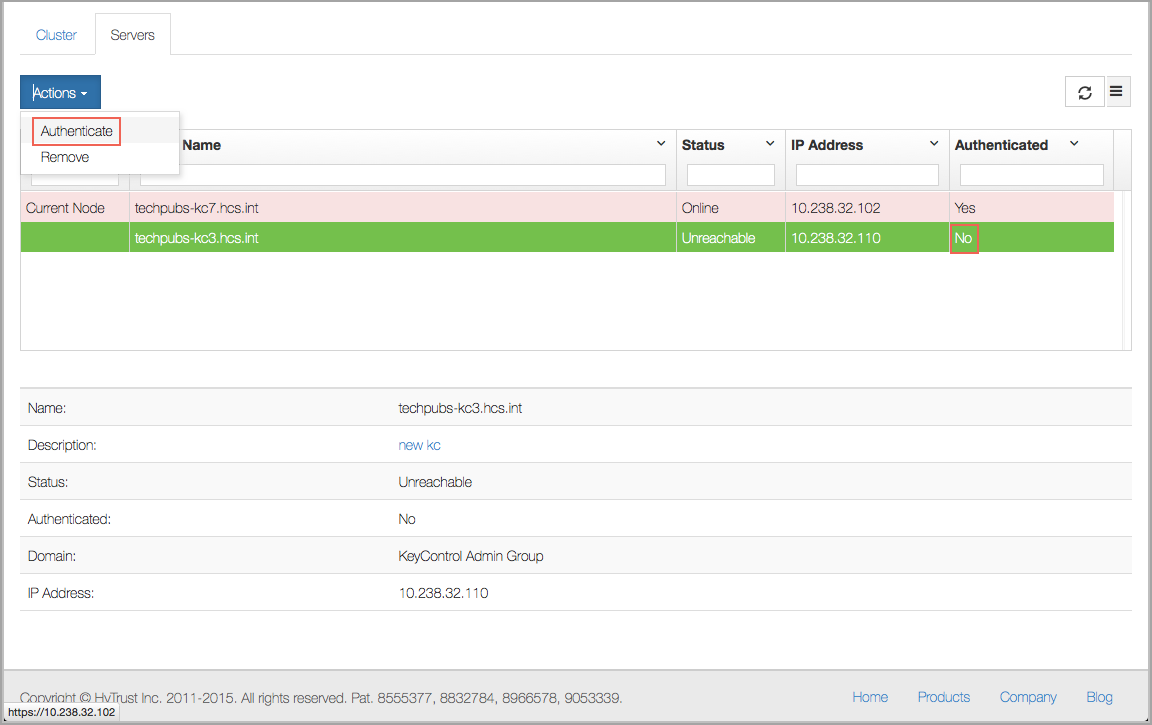
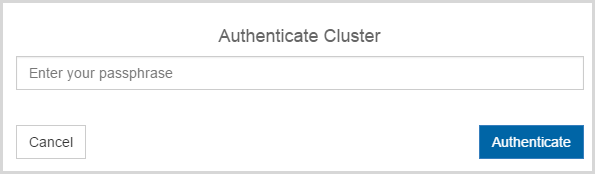
To authenticate this new node, click the Actions Button and then click Authenticate. This will take you to the authentication screen shown below. You are prompted to enter the Authentication Passphrase.
Once authentication completes, the KeyControl node is listed as Authenticated but Unreachable until cluster synchronization completes and the cluster is ready for use. This should not take more than a minute or two.
Once the KeyControl node is available, the status will automatically move to Online and the cluster icon will change from a red lightning bolt to a green heart with the number 2 inside of it, to indicate that there are two KeyControl nodes:

At this point, the new node is ready to use.